ModSecurity, also known as Modsec, is a free and open-source web application firewall for Apache webserver. ModSecurity is an Apache module that helps you to protect your web server from different types of attacks including SQL injection, XSS, trojans, bots, session capture/hijacking, and many more. ModSecurity provides powerful rule sets with real-time web monitoring, logging, and access control.
In this tutorial, we will show you how to install and configure Mod Security with Apache on Ubuntu 18.04.
Prerequisites
- A fresh Ubuntu 18.04 VPS on the Atlantic.Net Cloud Platform.
- A static IP address configured on your server.
Step 1 – Create an Atlantic.Net Cloud Server
First, log in to your Atlantic.Net Cloud Server. Create a new server, choosing Ubuntu 18.04 as the operating system with at least 2GB RAM. Connect to your Cloud Server via SSH and log in using the credentials highlighted at the top of the page.
Once you are logged into your Ubuntu 18.04 server, run the following command to update your base system with the latest available packages.
apt-get update -y
Step 2 – Install LAMP Stack
First, you will need to install LAMP Stack on your server. You can install it by running the following command:
apt-get install apache2 mariadb-server php7.2-mysql php7.2 libapache2-mod-php7.2 unzip git -y
After installing LAMP, start the Apache service and enable it to start after system reboot with the following command:
systemctl start apache2 systemctl enable apache2
At this point, the Apache web server is installed and running on your server.
Step 3 – Install ModSecurity
By default, ModSecurity is available in the Ubuntu 18.04 default repository. You can install it using the following command:
apt-get install libapache2-mod-security2 -y
Once the installation has been completed, restart the Apache service to apply the changes.
systemctl restart apache2
Next, you can also check whether the module has been loaded or not by running the following command:
apachectl -M | grep security
You should get the following output:
security2_module (shared)
Step 4 – Configure ModSecurity
There are no security rules configured by default, so you will need to enable it first. To do so, rename the ModSecurity default configuration file /etc/modsecurity/modsecurity.conf-recommended to /etc/modsecurity/modsecurity.conf.
cp /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf
Next, edit the file using your preferred text editor:
nano /etc/modsecurity/modsecurity.conf
Find the following line:
SecRuleEngine DetectionOnly
Replace it with the following:
SecRuleEngine On
Save and close the file when you are finished. Then, restart the Apache service for the changes to take effect.
systemctl restart apache2
Step 5 – Download and Configure ModSecurity Core Rule
ModSecurity’s default set of rules is available inside /usr/share/modsecurity-crs directory, but it is recommended to download a new rule set from the GitHub.
First, remove the old rules with the following command:
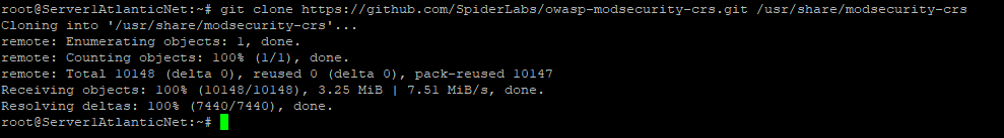
rm -rf /usr/share/modsecurity-crs
Next, download the latest rule set with the following command:
git clone https://github.com/SpiderLabs/owasp-modsecurity-crs.git /usr/share/modsecurity-crs
Next, you will need to enable this rule set in apache configuration. You can enable it by editing the file /etc/apache2/mods-enabled/security2.conf:
nano /etc/apache2/mods-enabled/security2.conf
Add the following lines above the line “</IfModule>”
IncludeOptional "/usr/share/modsecurity-crs/*.conf IncludeOptional "/usr/share/modsecurity-crs/rules/*.conf
Source: Securing Your Apache Web Server with ModSecurity
